
Welcome back!
Ready to check out?
You're just one click away from fantastic style and even better savings!
Determined to solve the case, John began to dig deeper. He reviewed the system logs, checked for any suspicious network activity, and even interviewed the IT staff. However, every lead seemed to end in a dead-end.
As they left the warehouse, John couldn't help but feel a sense of satisfaction. The mystery had been solved, and the company's systems were secure once again. He made a mental note to keep a closer eye on those hidden features in the Active Disk Image software.
John's mind was racing. He tried to keep the caller on the line, but they hung up. He quickly jotted down the phone number and started tracking it. To his surprise, the number led him to an abandoned warehouse on the outskirts of town.
As the day wore on, John became more and more intrigued. He decided to take a closer look at the Active Disk Image software itself. After some digging, he discovered a peculiar feature - a hidden "update key" function that could be accessed by a specific keyboard shortcut.
John's curiosity was piqued. He walked over to the computer and examined the screen. The software was indeed displaying an updated serial key, but there was no record of who had made the change. The company's IT team had strict protocols in place to prevent unauthorized changes, so this was a mystery.
Determined to solve the case, John began to dig deeper. He reviewed the system logs, checked for any suspicious network activity, and even interviewed the IT staff. However, every lead seemed to end in a dead-end.
As they left the warehouse, John couldn't help but feel a sense of satisfaction. The mystery had been solved, and the company's systems were secure once again. He made a mental note to keep a closer eye on those hidden features in the Active Disk Image software.
John's mind was racing. He tried to keep the caller on the line, but they hung up. He quickly jotted down the phone number and started tracking it. To his surprise, the number led him to an abandoned warehouse on the outskirts of town.
As the day wore on, John became more and more intrigued. He decided to take a closer look at the Active Disk Image software itself. After some digging, he discovered a peculiar feature - a hidden "update key" function that could be accessed by a specific keyboard shortcut.
John's curiosity was piqued. He walked over to the computer and examined the screen. The software was indeed displaying an updated serial key, but there was no record of who had made the change. The company's IT team had strict protocols in place to prevent unauthorized changes, so this was a mystery.
*Discount applied on the current website price at the time of order. Offer only valid for new customer first contacts order over $10. Maximum discount of $100. Cannot be combined with any other offers. Promotions are subject to change without notice. We reserve the right to cancel orders that are in breach of the terms and conditions of this offer.










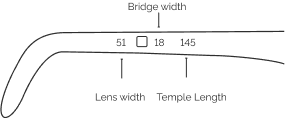
| Lens Width | Bridge Width | Temple Length | |
|---|---|---|---|
| XS | < 42 mm | < 16 mm | <=128 mm |
| S | 42 mm - 48 mm | 16 mm - 17 mm | 128 mm - 134 mm |
| M | 49 mm - 52 mm | 18 mm - 19 mm | 135 mm - 141 mm |
| L | >52 mm | >19 mm | >= 141 mm |
Buying eyewear should leave you happy and good-looking. Use our sizing tool to find frames that best fit your unique facial measurements.
Grab a regular card with a magnetic stripe on the back. Student IDs, credit cards and gift cards work well to start our online PD tool.
You may have received our paper PD measurement tool in your recent online order. In order to use this tool, place the ruler on your eyes so that the "0" lines up at the centre in between your eyes. Add up the two numbers, to get your PD. See example below:
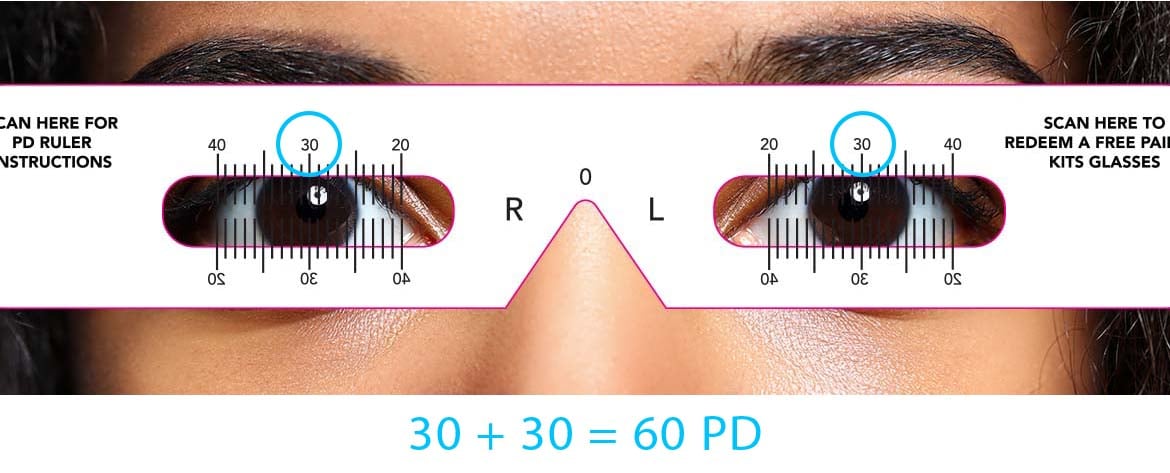
Click on this link to download and print your own PD measurement tool.
DOWNLOAD